One of the things I touched on in my last article for Freedom.Tech was the importance of understanding how Samourai Wallet worked in order to better understand the illogical premise these charges stand on, but we only briefly covered it.
In this post, we'll dive a bit deeper into the architecture of Samourai Wallet's app and services to get a grasp on why their service would normally be considered legal, what some of its weak points were, and help us better understand the case for and against Samourai right now.
Let's start from the ground up.
Samourai Wallet sync
At its core, Samourai Wallet was a self-custodial "light-client" Bitcoin wallet. What that means in practice is that users of Samourai Wallet always had full custody of their funds but users without their own node relied on a remote server – operated by Samourai Wallet – in order to get balances, check for received funds, and send transactions like many other Bitcoin wallets.
The default mode of Samourai Wallet is for a user's wallet to send their extended public key ("xpub") to Samourai's back-end server, allowing Samourai's server to check for any transaction history for the user and relay that information back to them. While this makes sync very fast for the end-user and low on bandwidth usage, it reveals all transaction data past, present, and future to Samourai Wallet and anyone else with access to the xpub.
The Samourai team stated that they only cached these xpubs temporarily when a user requested sync information, purging them after they were no longer needed and not storing them in perpetuity. To avoid this potential privacy leak, advanced users were able to either run their own back-end server (called a "Dojo") or use an alternate wallet that could still leverage Samourai's privacy tools called Sparrow Wallet. Both of these approaches did not reveal addresses or balance information to Samourai Wallet in any way.
You can read more below:
https://blog.ronindojo.io/most-whirlpool-users-run-dojo/
Whirlpool
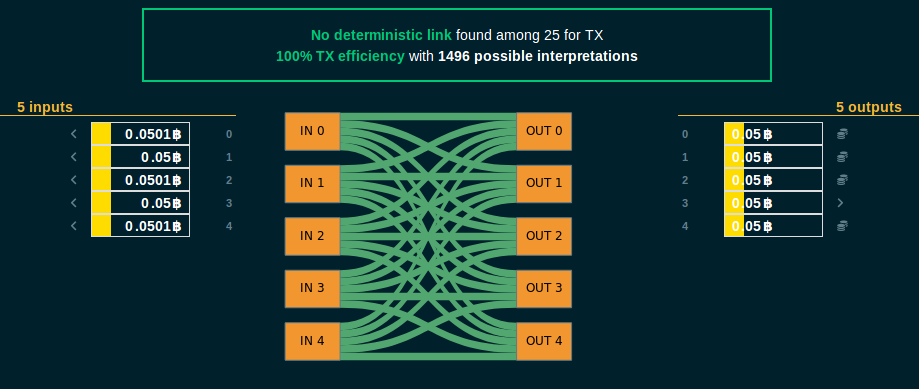
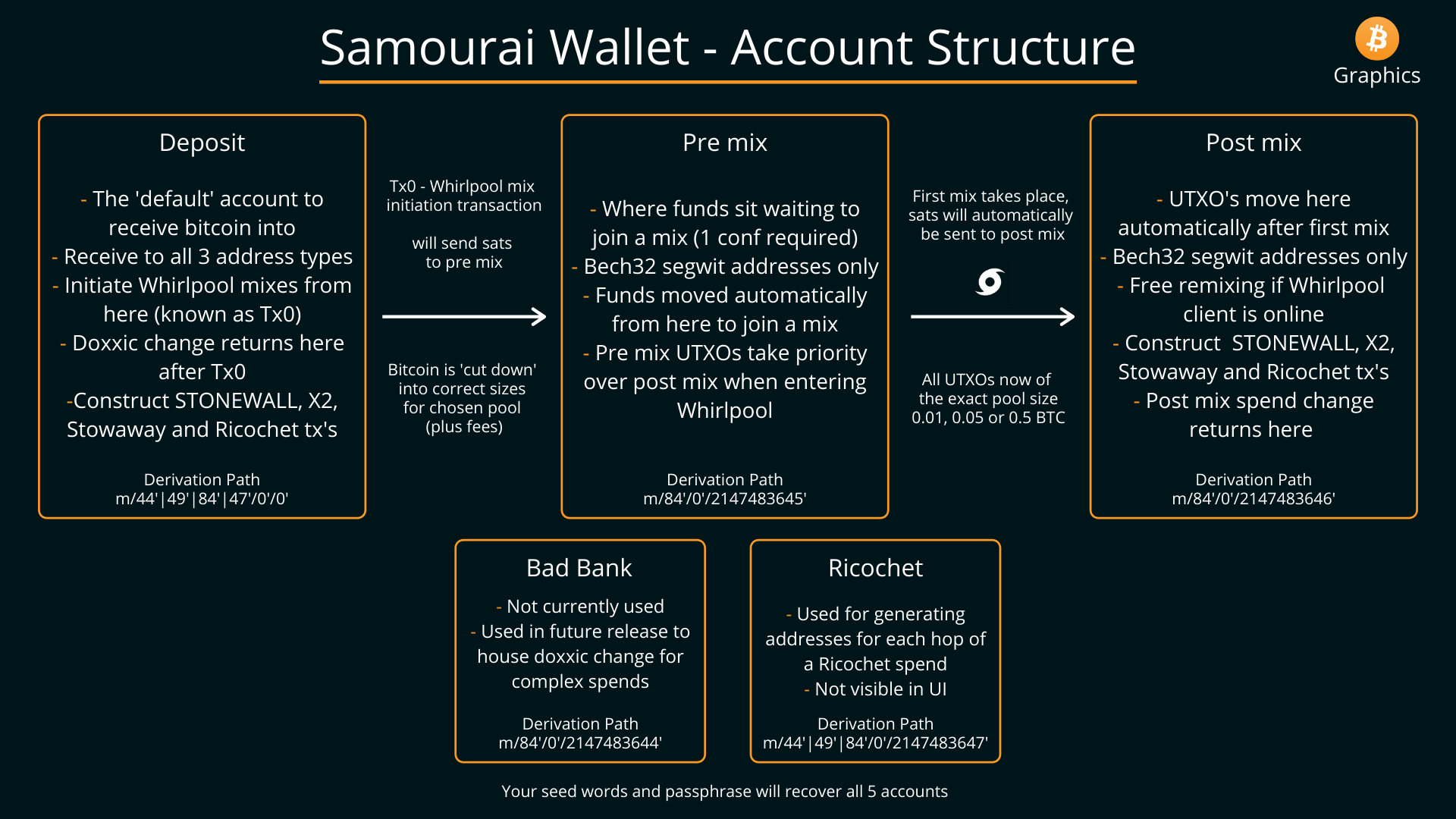
The core privacy tool offered by Samourai Wallet was known as "Whirlpool," and offered users the ability to break the deterministic (read: easily traceable) links between their past on-chain activity and future activity to outside observers. Whirlpool did this by bringing together 5 different users (or more, in what are called “surge cycles”) looking to gain privacy for the same-sized coin (i.e 0.01 BTC), helping them communicate their intent, and then allowing those users to construct and publish a collaborative transaction (also called a “CoinJoin”) together. When constructing these transactions, the 5 participants and coordinator work together in a way that does not reveal to them which participant receives which output, except their own.
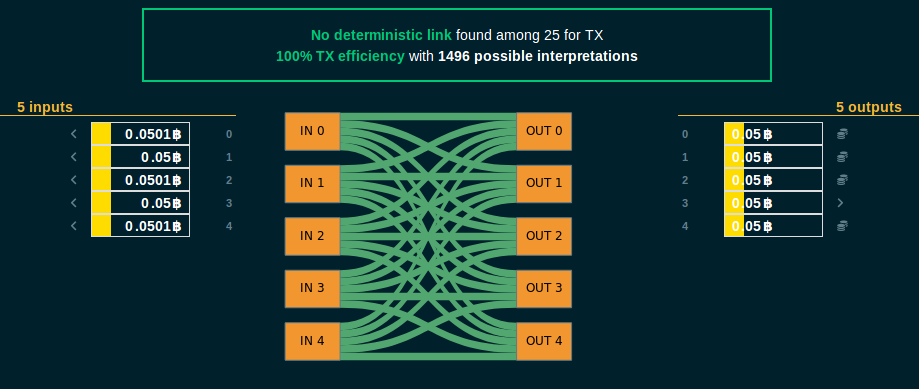
What is often misunderstood about Samourai is that a user never gives up custody of funds and never receives someone elses funds. At all times when searching for a mixing round, participating in a collaborative transaction, or broadcasting the transaction the owner of each input only has control over their own input, and no one elses. Samourai wallet’s role in this process is to “pool” liquidity, making it easier to find other peers who want to mix the same size inputs, assist in communication between peers, and broadcasting the final signed transaction. Essentially, Samourai Wallet’s coordinator server acted as a glorified bulletin board and message courier, and not a custodian or money transmitter.
The basic flow of a mixing round looked like this:
- A user submits an input they want to mix to the Whirlpool server over a unique, one-time Tor connection.
- The Whirlpool server approves the input’s registration.
- The user waits for enough peers to be found by the coordinator (usually four).
- Once enough peers are available, all peers in a round register their output with the coordinator.
- Once all outputs are registered, the coordinator sends a partially-signed Bitcoin transaction containing the registered inputs and outputs of all participants to each participant.
- Each participant validates that the PSBT sends their input to themselves as an output, and signs the transaction.
- Once all participants have signed the transaction, the Whirlpool server broadcasts the signed Bitcoin transaction to the Bitcoin network.
What is “remixing”?
Once a user has sent their initial inputs through a Whirlpool transaction, they can then either immediately send those funds somewhere else, or participate in what was called “remixing.” Remixing is the ability for Whirlpool users to queue up their already-mixed outputs to join in further rounds of Whirlpool to increase the privacy of their outputs by adding additional potential flows of funds. In order to incentivize better privacy over the long-term, Samourai Wallet did not charge a service fee or a mining fee for remixes, with all fees for each Whirlpool round being paid for by new, unmixed inputs.
Remixing was done primarily by those who ran their own Dojo back-end or utilized Sparrow Wallet, as remixing on mobile was difficult and inconsistent due to battery and network concerns. Remixing also meant that gaining strong privacy was something that happened over weeks or even months, and not overnight, a major hurdle if illicit actors sought to use Samourai Wallet for their purposes.
https://twitter.com/laurentmt/status/1783589772021071973
Ricochet
The other service mentioned in the indictment was the Ricochet spending tool. Ricochet allowed users to put “hops” between themselves and a final spend to a recipient, giving additional plausible deniability (and thus privacy) when transacting. Just like Whirlpool, this service never allowed Samourai Wallet to take custody of funds or alter the flow of funds at any point.
Note that there was the ability for Dojo users to manually schedule out transactions using the “TX Scheduler” tool in Dojo to avoid paying a fee or interacting with Samourai Wallet’s servers.
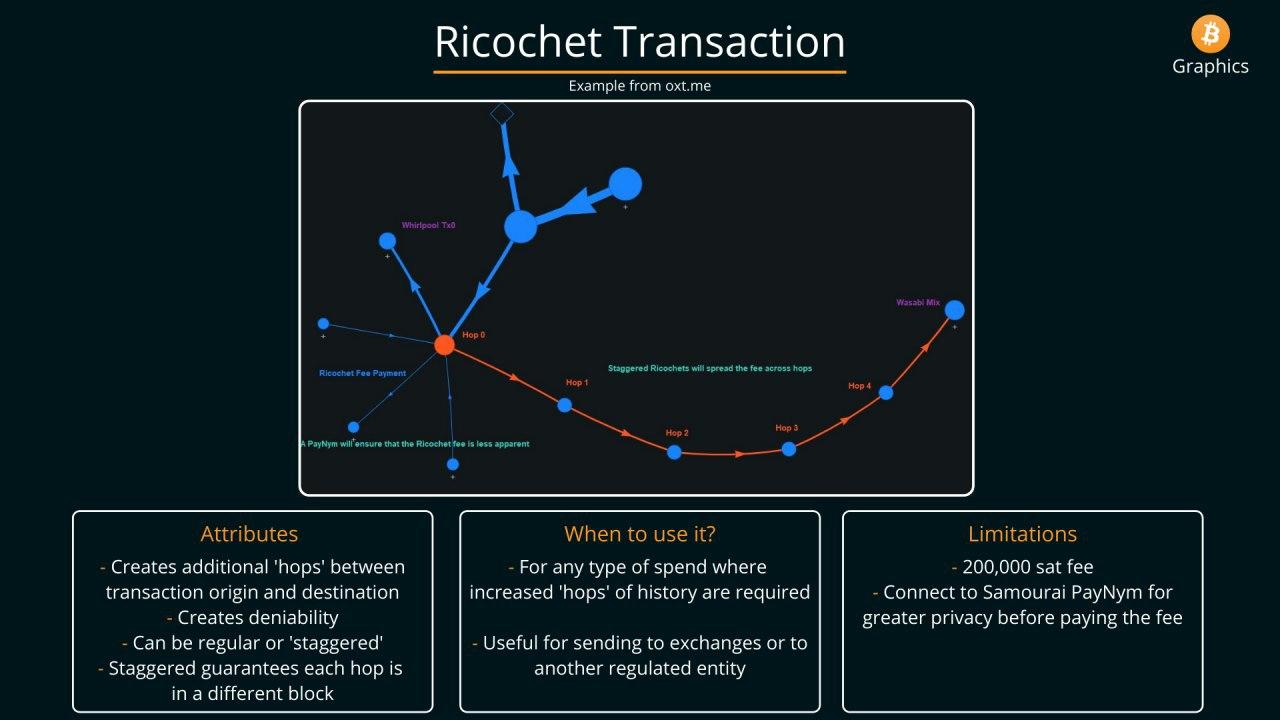
The basic flow of a Ricochet transactions looked like this:
- A user sets a destination address, if they want the transactions broadcast quickly or in a staggered manner, and provides the final destination address.
- A user’s wallet signs a set of Bitcoin transactions accomplishing this thread of transactions.
- The user’s wallet submits this set of pre-signed Bitcoin transactions along with a fee to the Samourai Wallet servers.
- Samourai Wallet’s servers simply accept the fee and broadcast the transactions requested by the user.
As all transactions are signed client-side, the server has no way to take custody of funds or alter the flow of funds in any way without invalidating the signatures on those transactions.
Other Samourai Wallet privacy tools
Even though the following tools were not explicitly mentioned in the indictment, it’s valuable to take some time to better understand how they worked and what role Samourai Wallet as an entity did or did not play in their function.
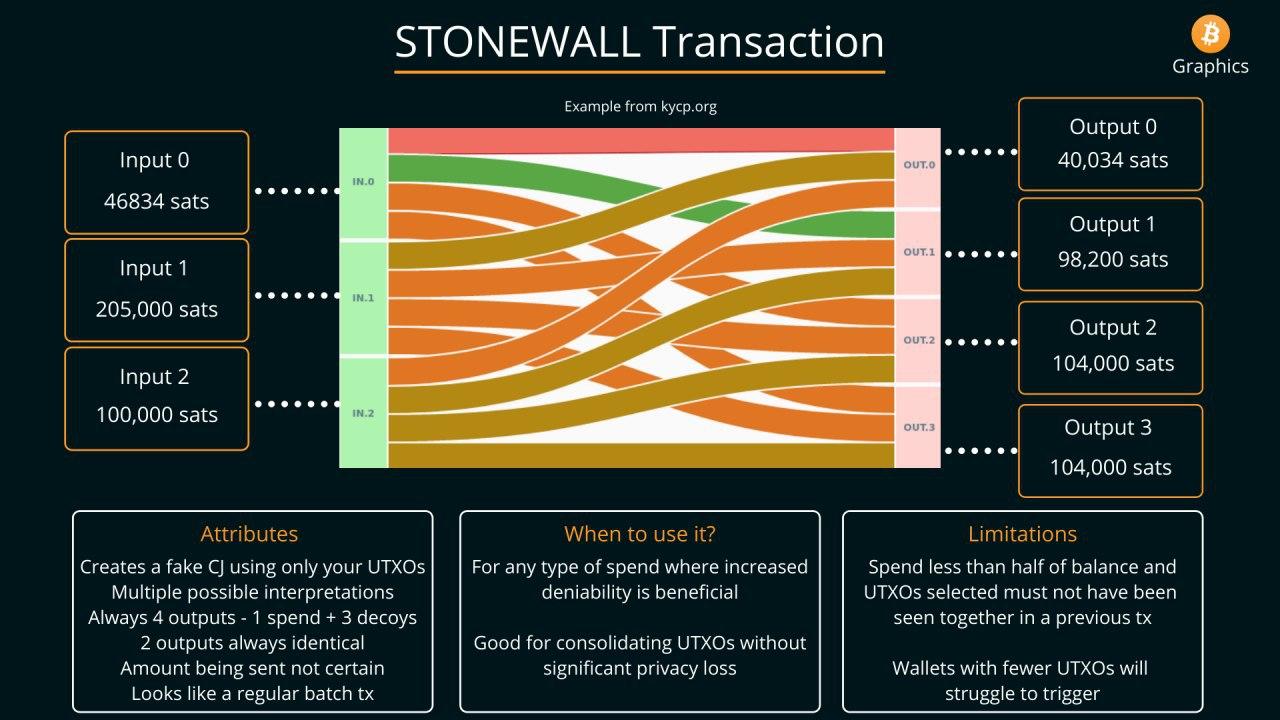
STONEWALL
STONEWALL was the default way that funds were spent in Samourai Wallet after going through Whirlpool (if the wallet had enough unspent coins). This transaction type did not involve any Samourai server or other peer, and occured entirely locally in the user’s wallet. Ultimately, a STONEWALL transaction created a “fake” 2-person collaborative transaction, giving additional plausible deniability on which input is linked to which output.
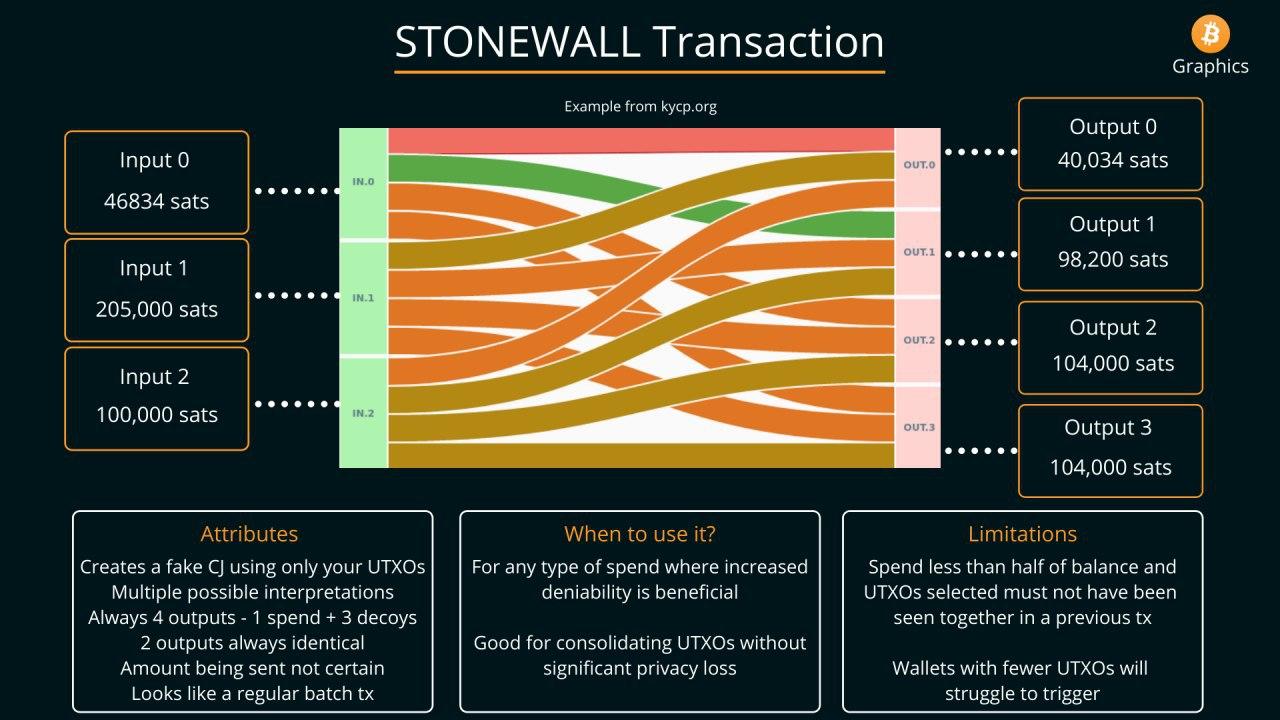
As STONEWALL transactions were all performed locally, Samourai Wallet of course could not take custody of funds or alter the flow of funds in any way.
STONEWALLx2
As the name implies, STONEWALLx2 is similar to a standard STONEWALL transaction, with the exception of actually involving another peer to create the transaction. This type of transaction obfuscated which inputs are owned by which entity, and where the funds ultimately are going.
STONEWALLx2 did not utilize any Samourai Wallet servers or services, and was directly coordinated by the two parties involved in the transaction, either in-person via a QR code exchange, or online via the Tor network. Users connected to each other using their PayNyms (a centralized directory of BIP 47 payment codes turned into usernames).
The only exception to this rule was the recent release of “Joinbot,” a service run by Samourai Wallet themselves that acted as the other peer in STONEWALLx2 transactions and collected a fee for the service. Even when Joinbot was used, Samourai Wallet could not alter the flow of funds or take custody.
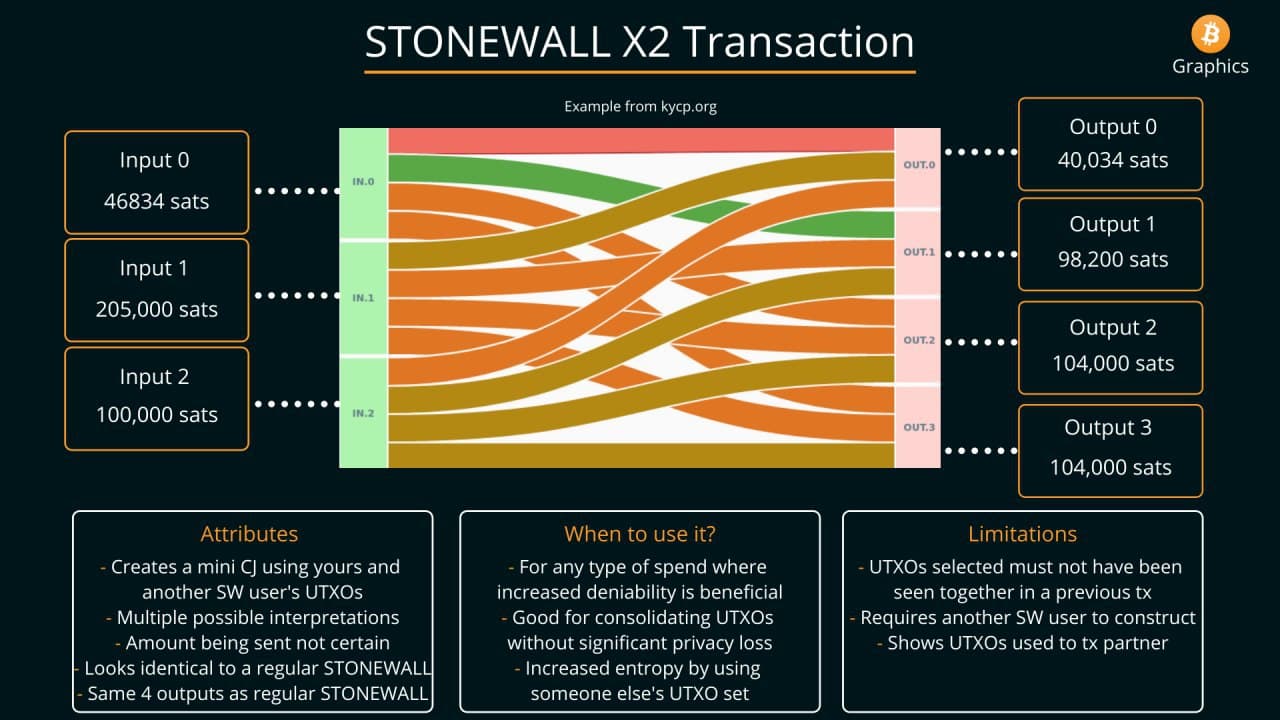
As STONEWALLx2 transactions were all performed peer-to-peer, Samourai Wallet of course could not take custody of funds or alter the flow of funds in any way.
STOWAWAY
STOWAWAY was an implementation of the concept behind PayJoins, a type of collaborative transaction that looks like a simple Bitcoin payment on-chain but actually involves two parties. Not only does STOWAWAY obfuscate the flow of funds, it also hides the amount being sent in a transaction. Just like in a STONEWALLx2 transaction, a STOWAWAY is entirely peer-to-peer, with users manually connecting to each other using PayNyms and communicating via the Tor network or an in-person QR code exchange.
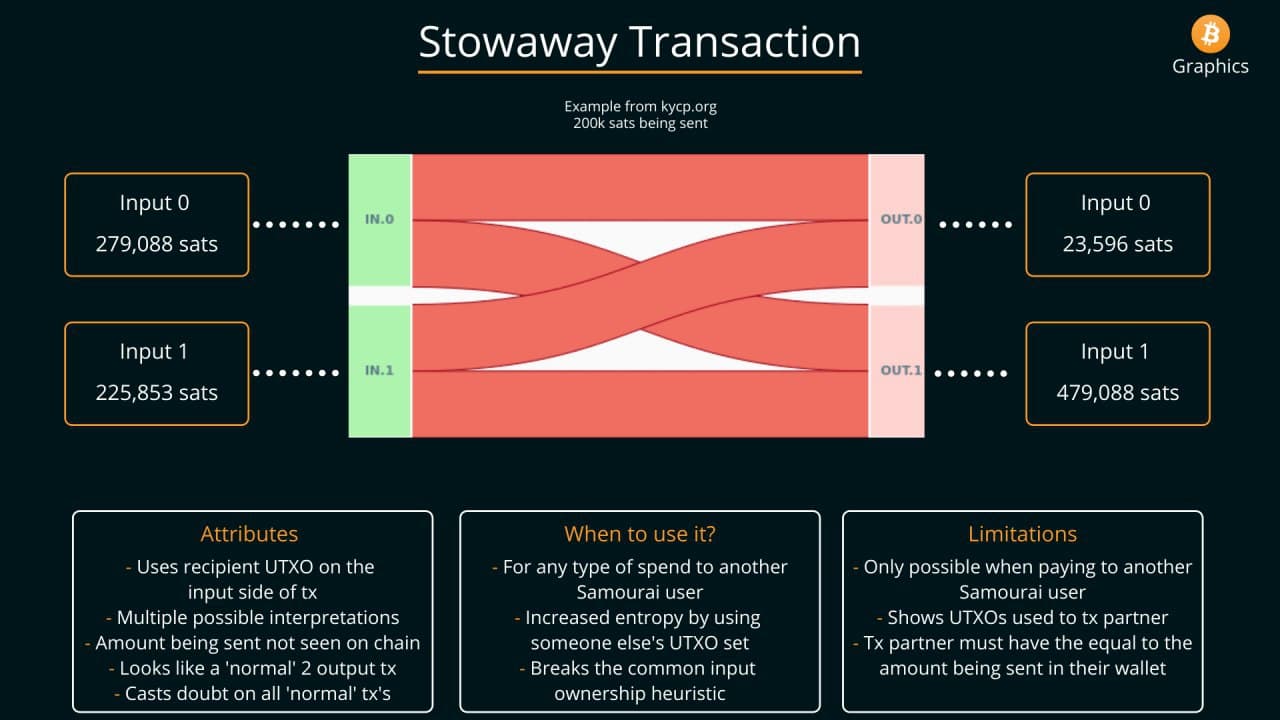
As STOWAWAY transactions were all performed peer-to-peer, Samourai Wallet of course could not take custody of funds or alter the flow of funds in any way.
Key takeaways
The vital thing to recognize about the functionality of Samourai Wallet’s app and services is that they never had the ability to take custody of user’s funds, never had the ability to alter the flow of funds, and ultimately acted as a simple message passer in functionality. When viewed in the light of the technical functionality of Samourai Wallet, the charges quickly fall apart.
Conspiracy to operate an unlicensed money transmission business
We’ve covered this specific charge at-length in our article on the Tornado Cash founder’s indictment by the DoJ, but by all previous legal precedent and regulation there are no grounds for considering a self-custodial wallet and service to be considered a money transmitter. From our previous article:
In a fantastic working paper released shortly after the indictment was unsealed, the International Academy of Financial Crime Litigators broke down what I think is the clearest view of FinCen’s money transmission definition (emphasis theirs):
“This brings to the forefront a crucial distinction: to act as a money transmitter, a party must have necessary and sufficient control over the value being transmitted.”
What is “necessary and sufficient control” you may ask? “Necessary control” in this case can be viewed as the tool being a required component of someone transmitting money. “Sufficient” control can be viewed as the owners of the tool having actual custody and ability to move deposited funds without user interaction.
While you can absolutely argue that Samourai Wallet’s app and servers had necessary control over the value being transmitted through their app when using the default back-end, and through Whirlpool, as they never took custody of user’s funds there is no grounds for considering them to have had “sufficient” control at any point in time. Thus, according to FinCen’s own definition they should not be considered a money transmitter in our view.
Conspiracy to commit money laundering
Similarly, the case of the DoJ on the charge of money laundering typically hinges on custody. It helps to use analogies in these situations to get a better grasp of the concepts in play, as we also did in our article on the Tornado Cash indictment:
To make the absurdity of this claim more vivid, let’s apply it to the use of cash to launder money. If any tool that is used in the act of money laundering is considered complicit, why don’t we also indict the makers of armored trucks that are used to move cash for banks? While armored cars may be necessary for banks to launder money, they never have sufficient control as the manufacturer doesn't take custody of funds – only the bank does.
Banks are by far the largest conspirators in the act of money laundering globally, and yet we don’t fault any of the service providers or manufacturers whose products are used in these money laundering schemes. Unlike most banking-related money laundering cases, however, the DOJ seeks to hold an individual accountable for merely building a tool that was allegedly used for money laundering by North Korean hackers.
While in this scenario armored car manufacturers do make an indirect profit off of creating a tool that could potentially be used in the act of money laundering, they are in no way held liable for the way their tool is used. So why should a service that never has custody over a users funds be considered a tool for money laundering?
It’s clear to me from the fact that the DoJ only seeks to bring conspiracy charges against the founders of Samourai Wallet that they are less concerned with what the Samourai Wallet app and service actually did and more concerned with expanding the reach of their financial enforcement arm through precedent instead of through legitimate legislation.
More resources
If you want to deep-dive into the architecture and details of how these tools functioned, the Samourai Wallet docs site is still live as of publishing. Below you can find detailed information on all of the tools mentioned today:
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:





